Blended Threat - Inscription on Blue Keyboard Key Stock Image - Image of network, service: 177568647
BLENDED ATTACKS EXPLOITS, VULNERABILITIES AND BUFFER-OVERFLOW TECHNIQUES IN COMPUTER VIRUSES By: Eric Chien and Peter Szor Presented by: Jesus Morales. - ppt download

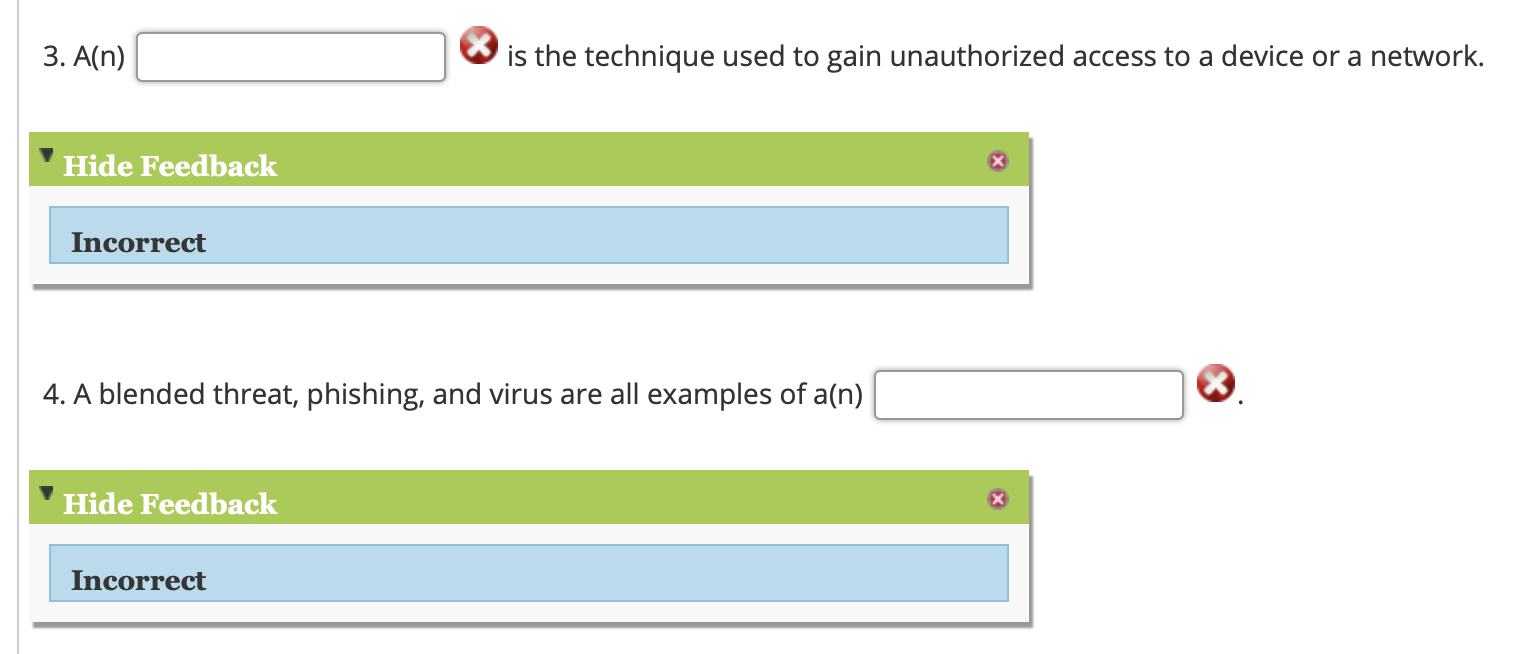
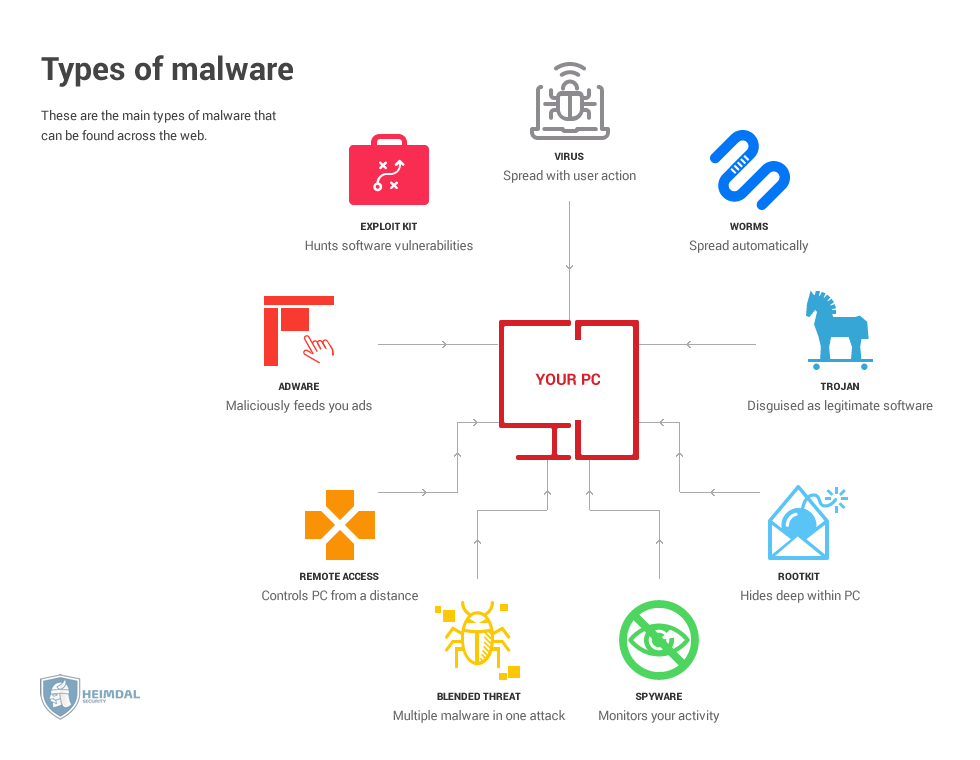
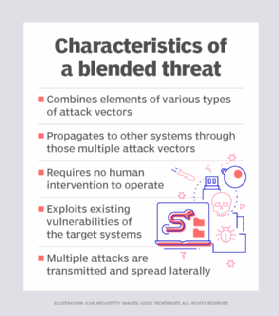
Whiz Security - Blended Threat A blended threat is an exploit that combines elements of multiple types of malware and usually employs multiple attack vectors to increase the severity of damage and